Mirador
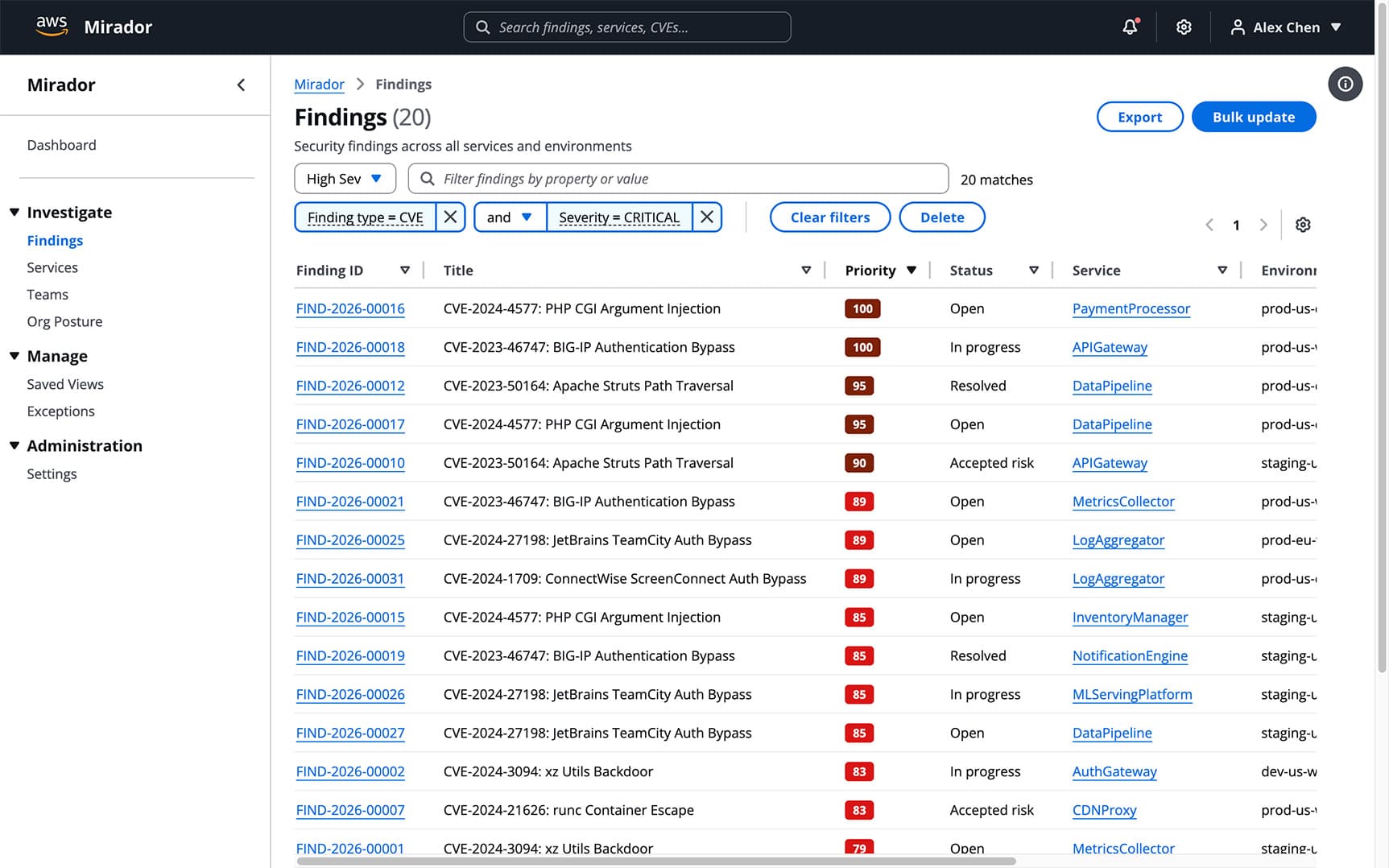
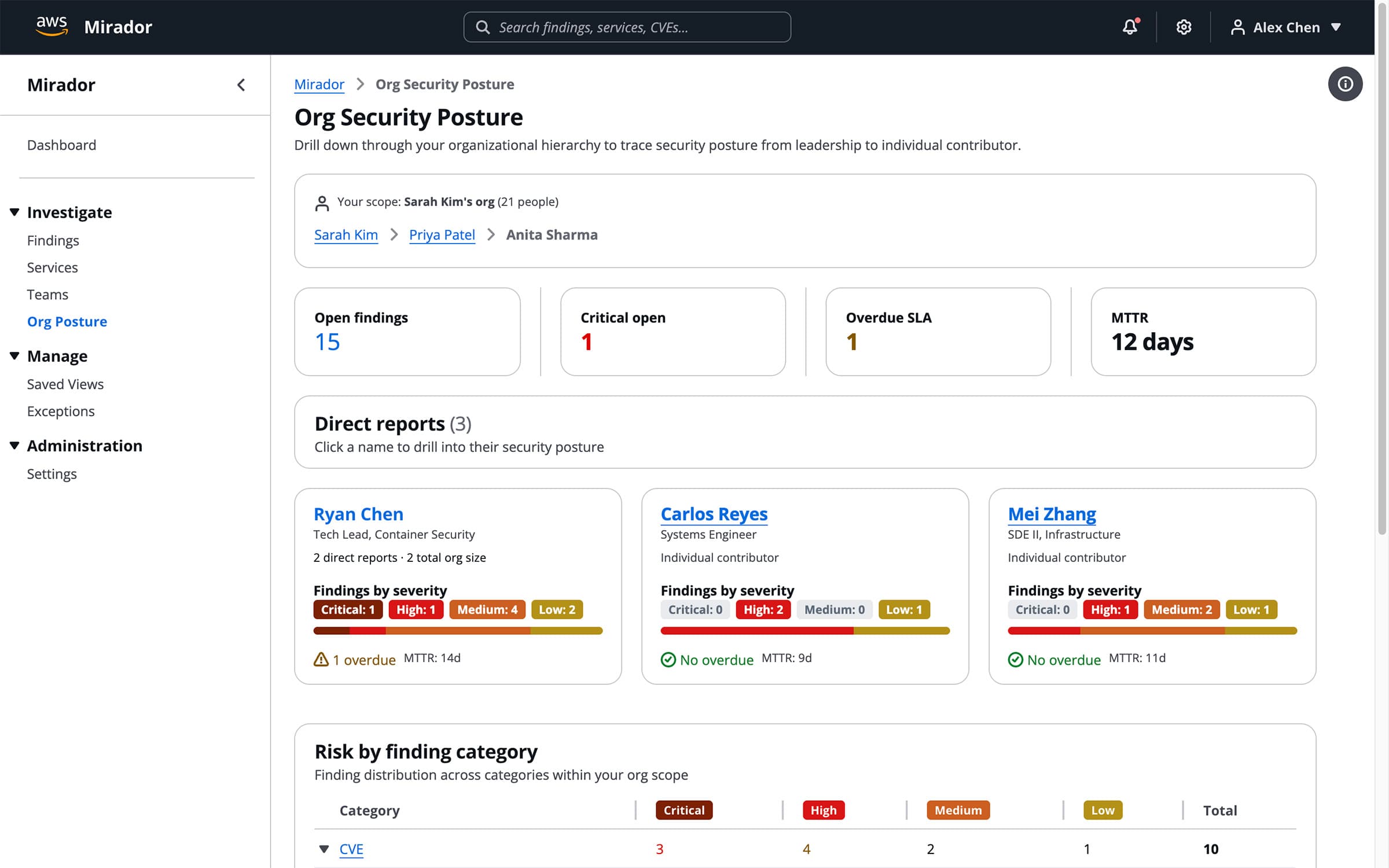
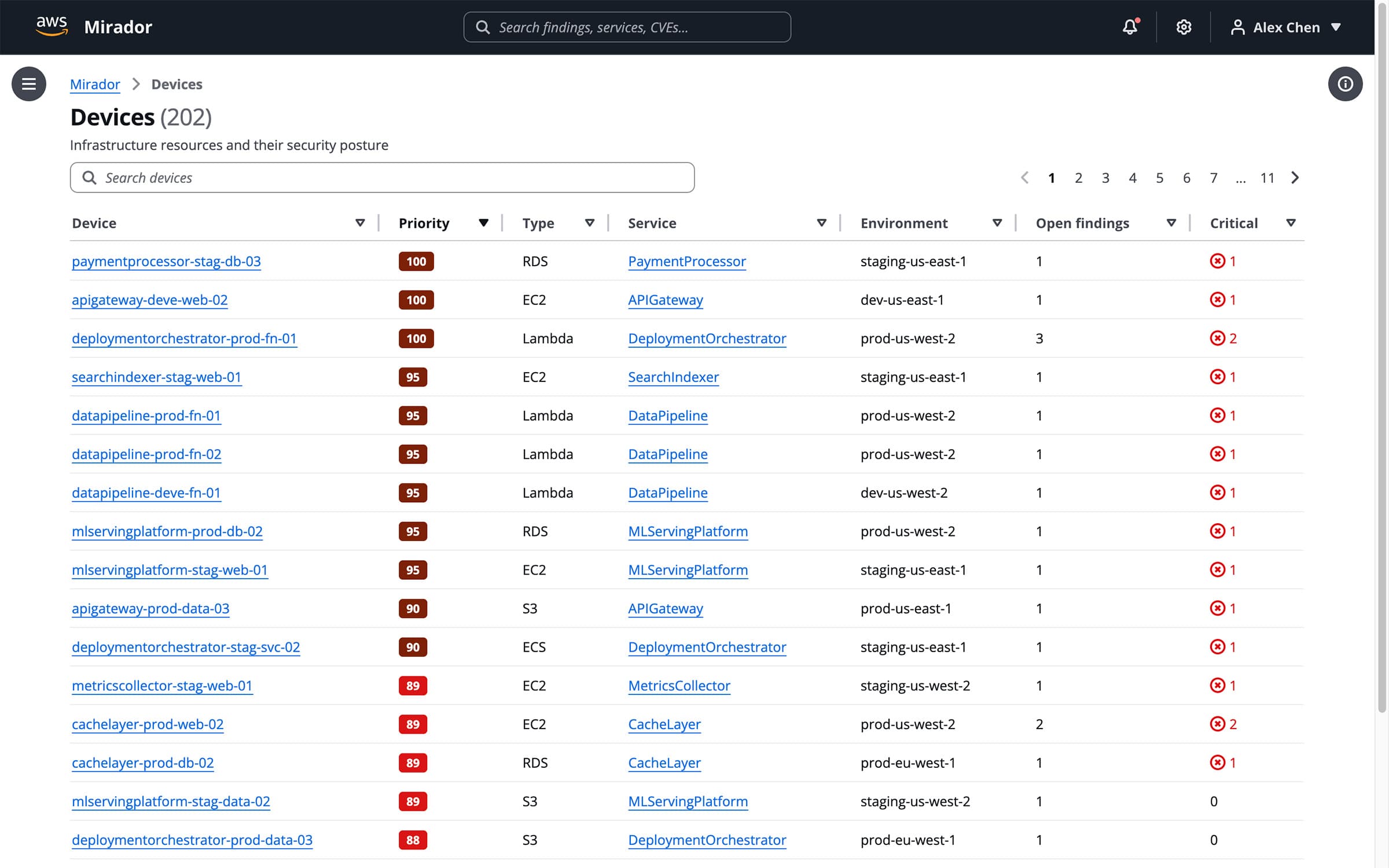
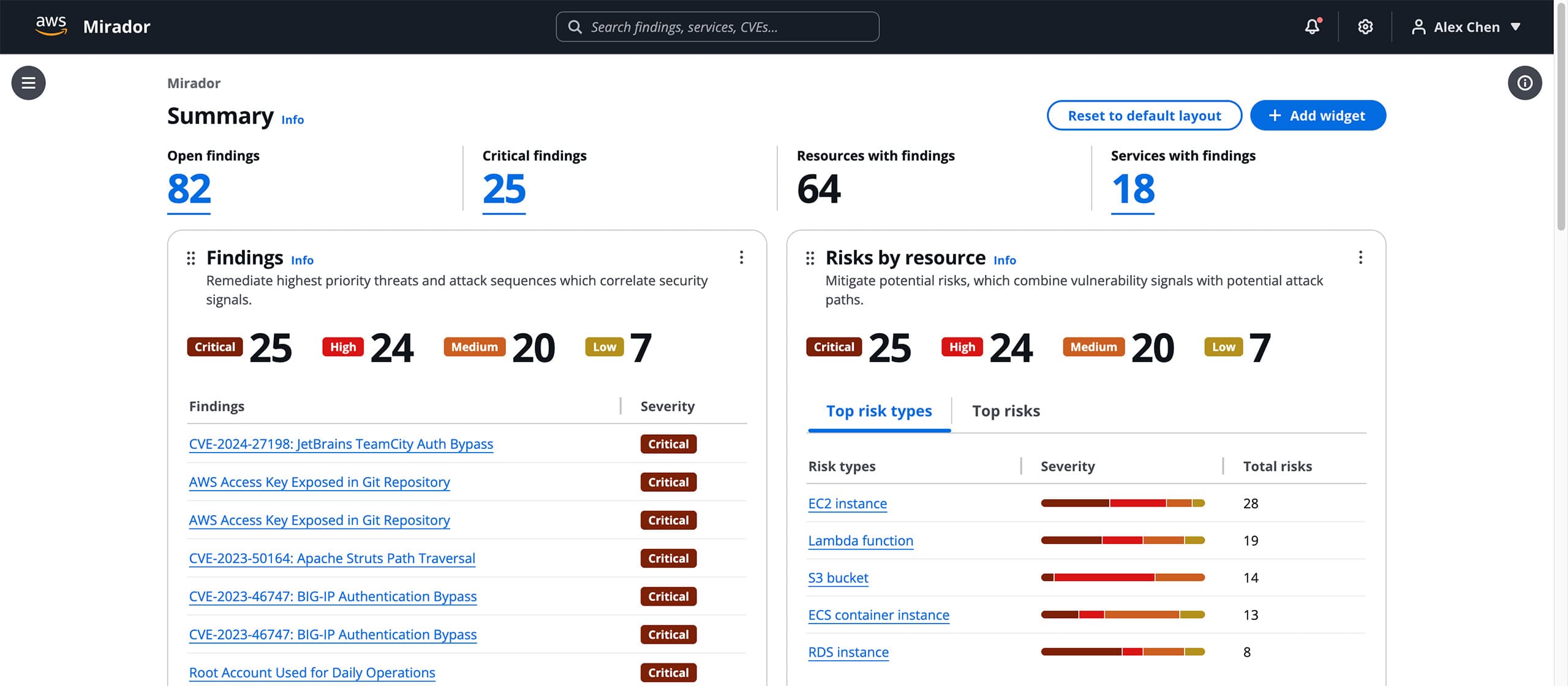
Mirador is AWS’s internal security posture platform. As the sole designer, I replaced six fragmented tools with a single unified dashboard. The platform rolled out company-wide in Q4 2024, fully retiring all legacy tools, with a 4.6/5 task satisfaction score.
- 6 legacy tools replaced
- 4.6/5 task satisfaction
- Company-wide rollout
- Product Manager
- Engineering Lead
- 1 Front-end Developer
- 11 Engineers
Senior UX Designer (Sole Designer)
The Problem

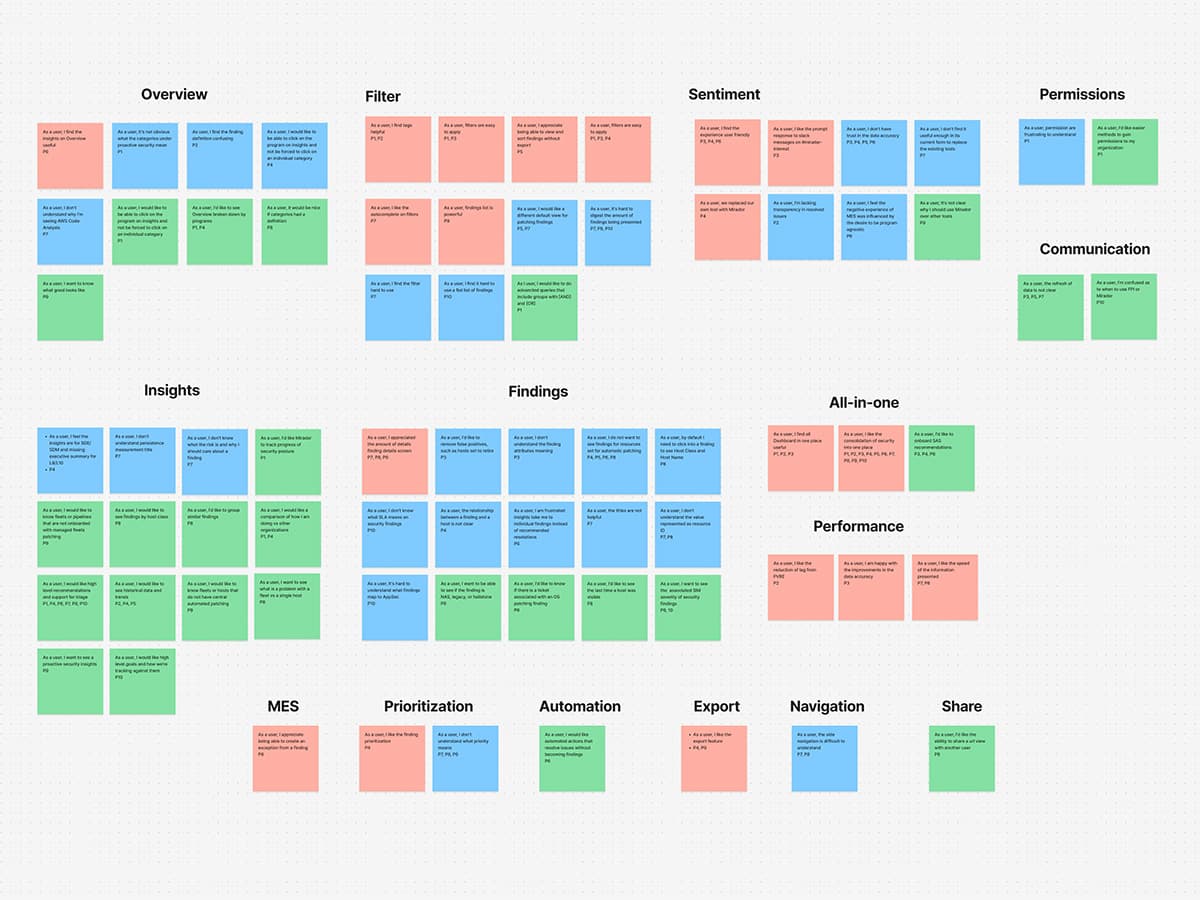
Discovery
From Andy Jassy to Individual Contributor
Saved Filters: From Mirador to the Entire Design System
Device View, Vulnerability View, Criticality View
Validation
Mirador shipped company-wide in Q4 2024. All six legacy tools were fully retired. Usability testing averaged a 4.6/5 satisfaction score across core tasks. The saved filter component was adopted into the Cloudscape design system and is now used by 300+ designers across AWS. The platform remains in active use today.